
Technology has enabled today’s workforce to become increasingly mobile. Your company may have employees in numerous locations across the country. And even if it doesn’t, odds are you and your employees do at least some of your work outside the confines of your office — whether from home, coffee shops, or customer locations.
Unfortunately, cybercriminals have also developed sophisticated ways to use this increased mobility to gain access to your network and your data. Thankfully, there is a security measure that can drastically reduce the risk of a breach while still allowing for mobility — a Virtual Private Network (VPN).
If your employees work remotely, hopefully you have systems in place to allow employees to “remote in” to your company network. That way, they can access company data and use company software resources “at the source,” so to speak, rather than creating duplicates on employee devices, which are inherently less secure.
This remote access is usually handled through protocols, such as Windows Remote Desktop Protocol (RDP), that allow a user to access a “remote desktop” within the company’s internal network. The only problem is that allowing your employees to access your company network using protocols like RDP often involves opening your network to the entire internet. Your employees have to be able to access it from anywhere, so your firewall has to allow anyone to navigate to an address that grants access to your network.
True, RDP does have basic security features, such as a username and password, that prevent just anyone from accessing your network. These measures used to be viewed as sufficient by industry standards. The problem, though, is that passwords have become increasingly easy for hackers to crack or steal through social engineering. Remote connections to your office, then, pose a significant risk for a breach.
Thankfully, there is a way for businesses to continue using protocols like RDP without leaving the company network vulnerable – through VPNs
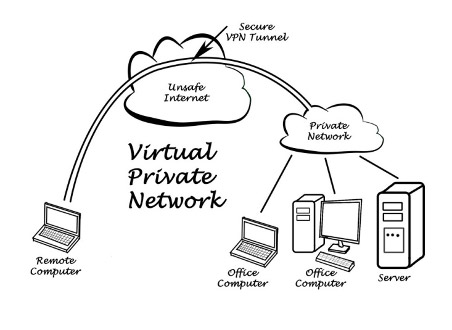
We often explain VPNs to clients by comparing them to a secure, virtual Ethernet cable that plugs a remote user’s device—whether it’s in their home or in a coffee shop—directly into the company’s internal network. As depicted below, VPNs create encrypted “tunnels” between a user’s computer or mobile device and a server connected to the internet.
This means that no one between the user and the server they are connecting to can gain access to the data that is being transmitted. All the user has to do is turn the VPN “on.”
We recommend that businesses who want to provide remote access to company resources use VPNs because they remove the need for leaving a network open to all outside traffic. Whereas without a VPN a business would have to open parts of their network to expose internal resources so that employees could log in, VPNs allow a secure way for employees to log into the network, through protocols like RDP, without it having to be open to the public.
Cybercriminals, then, won’t be able to see your company’s remote server on the internet, and they won’t be able to intercept communications between your employees and your network. This has the added bonus of making it safe for employees to work while using public WiFi. It’s pretty easy for criminals to create “fake” WiFi hotspots, or gain access to users’ data over unprotected hotspots. But with a VPN, all traffic between the company server and the user is encrypted, meaning a WiFi hacker wouldn’t have access to it.
As with many technical innovations that begin life as tools for business use, VPNs have gone “mainstream” with numerous options available for consumer use. Consumers use them to add a layer of security when using public Wi-Fi, or just to create a more private connection to the internet.
These consumer VPN products are different from the VPNs we implement for business clients in a few ways. Firstly, not all VPNs are created equal; some of them are configured to use outdated encryption methods (such as PPTP), meaning that they are insecure. Secondly, consumer VPN services involve creating a VPN between the customer’s computer and the vendor’s servers, from which the customer can then access the internet. Consumer VPNs, then, are only as secure as the vendor is trustworthy, and they cannot be used to create remote connections to a company’s office.
The business-class VPNs we set up for our clients, by contrast, always involve industry-standard encryption and create a direct connection between the employee’s computer and the company’s network (which is necessary for allowing remote access)—as opposed to involving a third party. It’s critical, then, that businesses work with reputable IT professionals to set up their own VPNs, as opposed to using consumer products.
If you or your team members are connecting to your office remotely without a VPN, your data is at risk. If you’re ready to explore whether a VPN could boost your security, contact us today. We’d love to discuss the benefits with you in person, and even demonstrate how the technology works!
Centuria Office Park, Unit 8,
265 Von Willich Street,
Centurion